Intrazone — East/West Protection¶
Intrazone strategies apply microsegmentation inside a clearly bounded network zone (one or more subnets, or a DMZ).
The main objective is to reduce lateral movement by controlling East/West traffic (workload-to-workload) within that zone.
Core principles¶
- The zone is typically protected by a physical perimeter firewall.
- North/South traffic (entering/leaving the zone) is handled primarily by the perimeter firewall.
- East/West traffic inside the zone is enforced by Illumio:
- ALLOW only if explicitly permitted
- DENY by default for non-authorized lateral paths
Tip
Intrazone is often the fastest way to get strong containment in a DMZ without redesigning North/South controls.
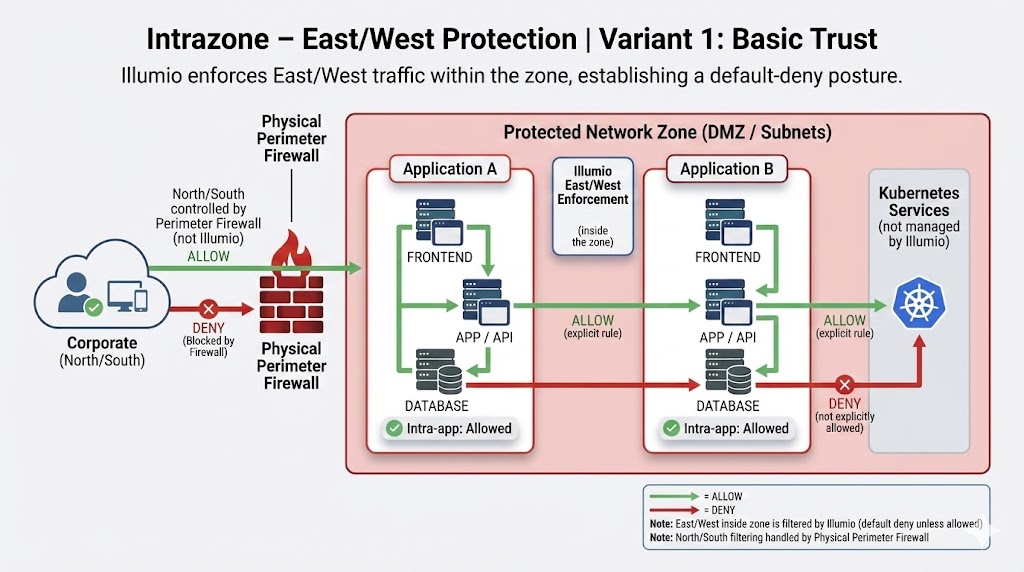
Variant 1 — Basic Trust¶
This variant focuses on East/West enforcement inside the zone while keeping North/South filtering at the perimeter.
What it demonstrates¶
- A Protected Network Zone (DMZ / subnets) behind a physical firewall
- Two Applicative Bubbles inside the zone
- East/West flows are filtered by Illumio:
- only explicitly allowed flows are permitted (green)
- everything else is denied (red)
- If a server inside a bubble is not equipped with the Illumio agent, it becomes effectively isolated from the zone
- The zone may host unmanaged elements (e.g., Kubernetes services) while traffic to/from them remains policy-controlled by Illumio
Warning
Unmanaged workloads may become isolated by design. Confirm onboarding coverage before enforcing strict East/West policies.
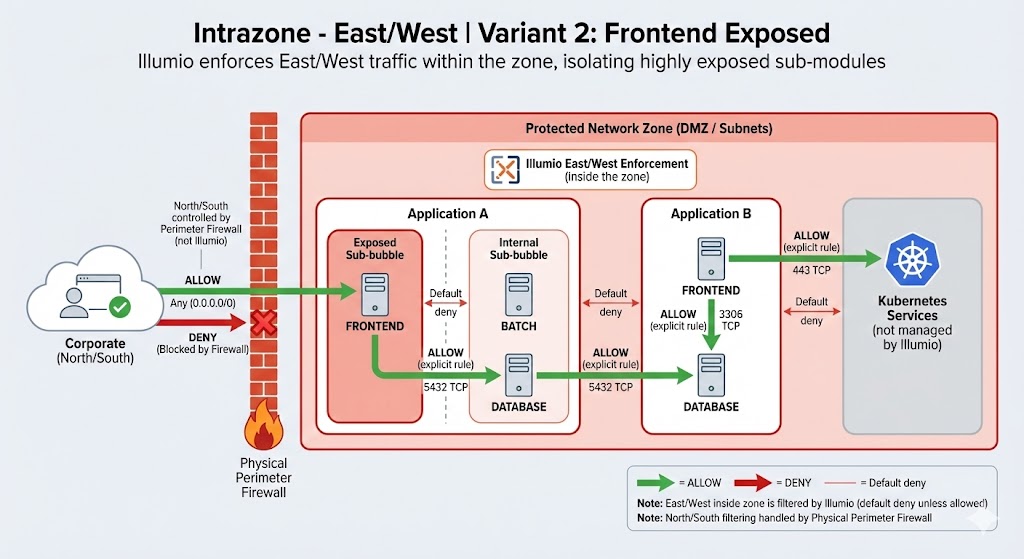
Variant 2 — Frontend Exposed¶
This variant is suited when the zone contains a frontend that is reachable from North/South, while you still need strong containment of East/West inside the zone.
What it demonstrates¶
- North/South exposure to the frontend is governed by the perimeter firewall
- Illumio continues to enforce East/West inside the zone:
- frontend → app and app → database require explicit allows
- “pivot” paths (unexpected lateral movement) are denied
When to use Intrazone¶
- You can define a bounded zone (DMZ / subnet sets)
- You want immediate reduction of lateral movement inside that zone
- You want to keep North/South governance at the perimeter while adding workload-level East/West control
Operational notes (high level)¶
- Define the zone scope and map the applications inside it
- Start with the minimum explicit allow rules required for operations
- Validate onboarding coverage to avoid unintended isolation