Fine-grained Strategies¶
Fine-grained strategies introduce explicit control across application boundaries.
They help you build a scalable model where dependencies are clear, auditable, and least-privilege oriented.
Fine-grained IN/OUT (Ingress + Egress)¶
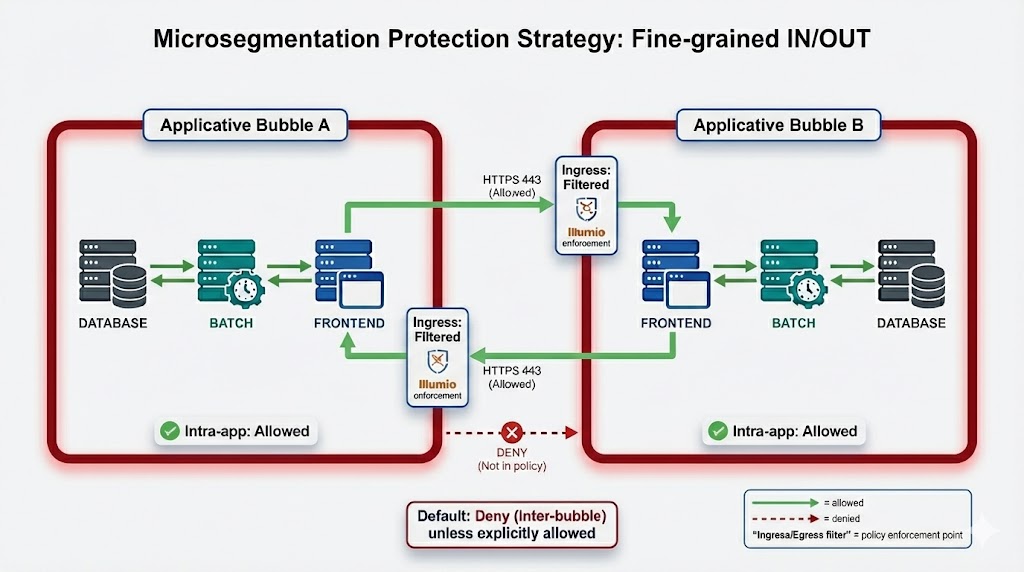
This strategy treats each application as an Applicative Bubble (a logical perimeter defined by labels/scope).
Core principles¶
- Intra-app traffic (within the same bubble) is initially ALLOWED to preserve functionality during early rollout.
- Ingress is FILTERED: only explicitly allowed flows may enter the bubble.
- Egress is FILTERED: only explicitly allowed flows may leave the bubble.
- Inter-bubble default = DENY unless there is an explicit allow rule.
Why it is valuable¶
- Makes application dependencies explicit (who talks to whom, on which ports)
- Reduces exposure by controlling both entry and exit paths
- Provides a clean foundation for long-term least privilege
When to use Fine-grained¶
- You want strong, scalable least-privilege controls between applications
- You need clear dependency mapping and auditable enforcement
- You can operationalize an allow-list model (ownership, validation, iteration)
Operational notes (high level)¶
- Define stable application scopes (labels) and keep them consistent over time
- Start with the minimum explicit rules you can justify and validate
- Iterate based on observation, owner validation, then tighten
Next variant (planned)¶
Note
We will add an additional Fine-grained variant later: Inbound-focused
- Outbound: allow all
- Inbound: filtered on selected applicative ports with Any as source