Team Organization — Operating Model¶
This section explains how the Microsegmentation team is organized to deliver a reliable service to users while keeping delivery fast, predictable and compliant.
Why this organization works for users¶
Our users (application teams, security stakeholders, and operational teams) typically need one of the following outcomes:
- Onboard an application into microsegmentation (flows → rules → first protection)
- Change or extend an existing policy safely (controlled change)
- Keep protection sustainable in RUN (agents, upgrades, monitoring, DR exercises, audits)
- Get better tooling and reporting (automation, quality controls, portal)
This operating model is designed to address these needs through:
- Clear ownership (one team leads each major activity)
- Explicit handovers (defined inputs/outputs, DoR/DoD gates)
- ITIL-aligned governance (incident/change/problem/knowledge)
- Continuous improvement via automation and product delivery
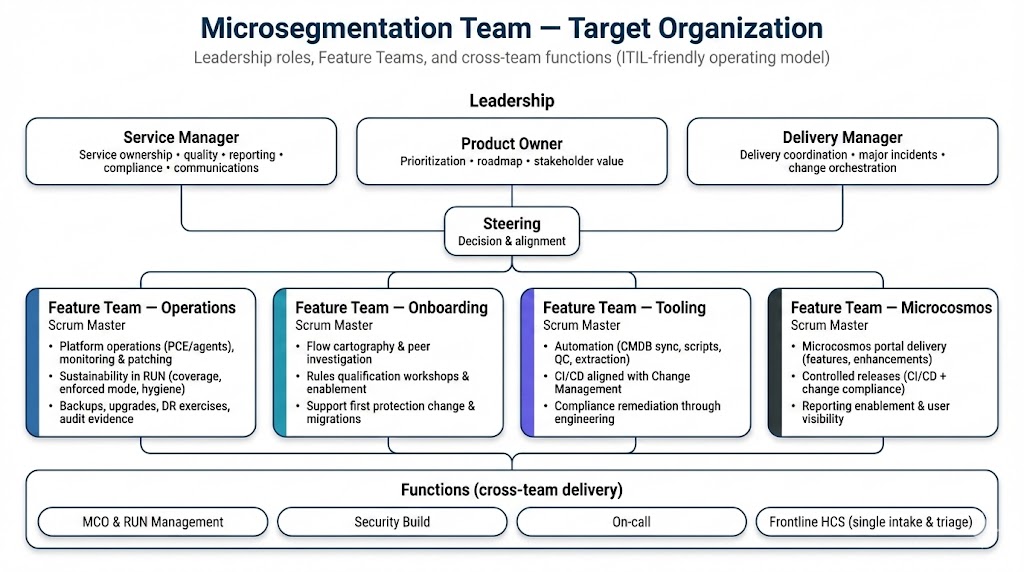
Target organization (high level)¶
Leadership roles
- Service Manager — service ownership, quality, reporting, compliance, communications.
- Product Owner — prioritization, value management, roadmap, stakeholder alignment.
- Delivery Manager — execution coordination, delivery predictability, major incidents & change orchestration.
Feature Teams - FT Operations — platform operations & sustainability in RUN. - FT Onboarding — security build & enablement (flows to first protection). - FT Tooling — automation and DevOps engineering to scale delivery. - FT Microcosmos — portal product delivery and reporting enablement.
Cross-team functions - MCO & RUN Management, Security Build, On-call, Frontline HCS (single entry + triage).
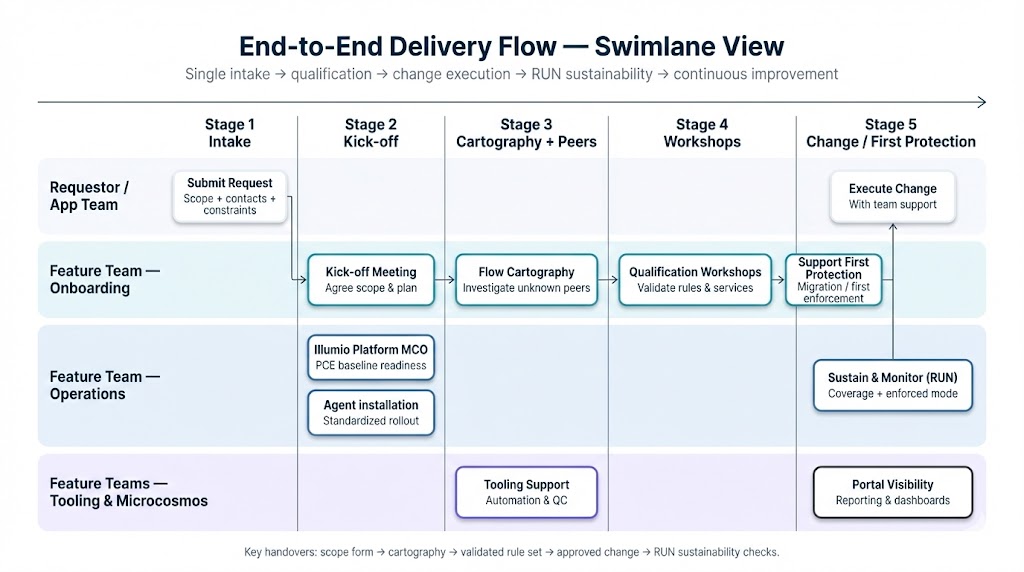
End-to-end delivery flow (swimlane)¶
What the swimlane ensures for users¶
-
One predictable intake
Users know where to go, and the team knows how to triage. -
Faster onboarding (less back-and-forth)
FT Onboarding drives kick-offs, cartography, peer investigation and workshops. -
Safer change execution
Changes use standard templates where possible; CRB/CAB gates are applied when required. -
Stable RUN with sustainability checks
FT Operations ensures agent coverage, enforced coverage (RUN apps), upgrades, monitoring, backups, DR exercises and audit evidence. -
Continuous improvement through engineering
Tooling and Microcosmos reduce manual work and increase transparency.
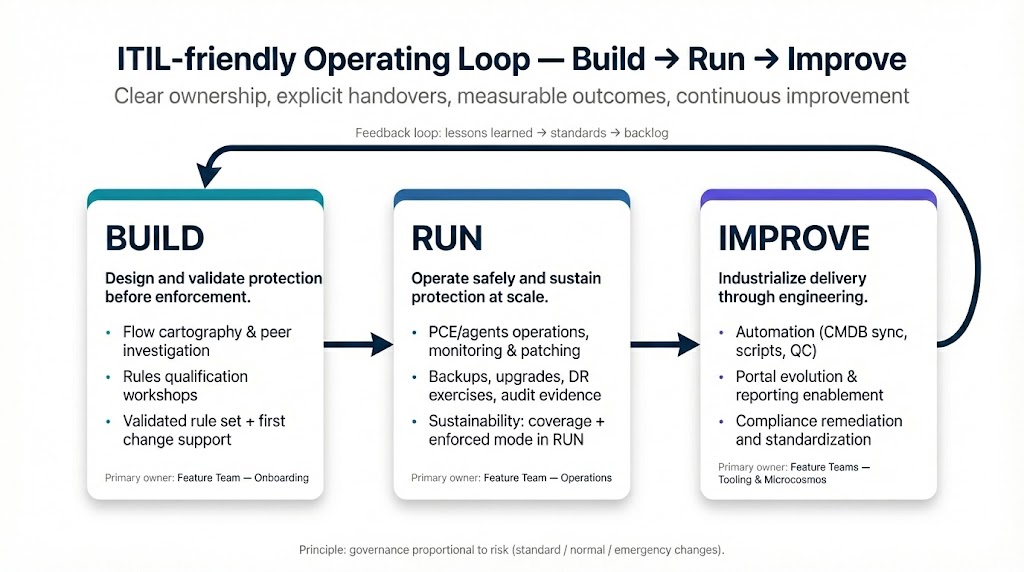
ITIL-friendly operating loop: Build → Run → Improve¶
Build (FT Onboarding) - Flow cartography & peer investigation - Rules qualification workshops - Support for first protection change / migration - Core services validation (Bouquets Infra / committee)
Run (FT Operations) - PCE/agent operations, monitoring and patching - Backups, upgrades, DR exercises - PCE object hygiene and quality (labels, naming, pairing lifecycle) - Sustainability: agent coverage and enforced mode for RUN applications
Improve (FT Tooling + FT Microcosmos) - CMDB sync batch, admin scripts, daily QC & drift detection - Cartography scripts and ruleset extraction tooling - Microcosmos portal enhancements, controlled releases - Compliance remediation through automation and product evolution
Engagement model (how to work with us)¶
1) Single intake (Frontline HCS)¶
- Purpose: ensure fast routing to the right team and avoid “lost requests”.
- Output: a clear scope + assignment to the owning feature team.
2) Delivery with explicit handovers¶
We use simple handover rules to reduce ambiguity:
- DoR (Ready): scope defined, contacts identified, target timeline agreed.
- DoD (Done): evidence produced, runbooks/knowledge updated, stakeholders informed.
3) Governance proportional to risk¶
- Standard changes (pre-approved templates) → fast and repeatable.
- Normal changes → reviewed in CRB/CAB as applicable.
- Emergency changes → accelerated path + retrospective.
What success looks like (user outcomes)¶
- Shorter onboarding cycle time (request → validated rules → first protection)
- Higher first-change success rate (less rework, less rollback)
- Better RUN stability (lower incident rate, faster MTTR)
- Higher sustainability (agent/enforced coverage for RUN applications)
- Less manual effort (automation, QC, portal visibility)