What is microsegmentation?¶
Microsegmentation is a zero-trust approach that controls connectivity between application servers (workloads) at a very granular level (per application, environment or role).
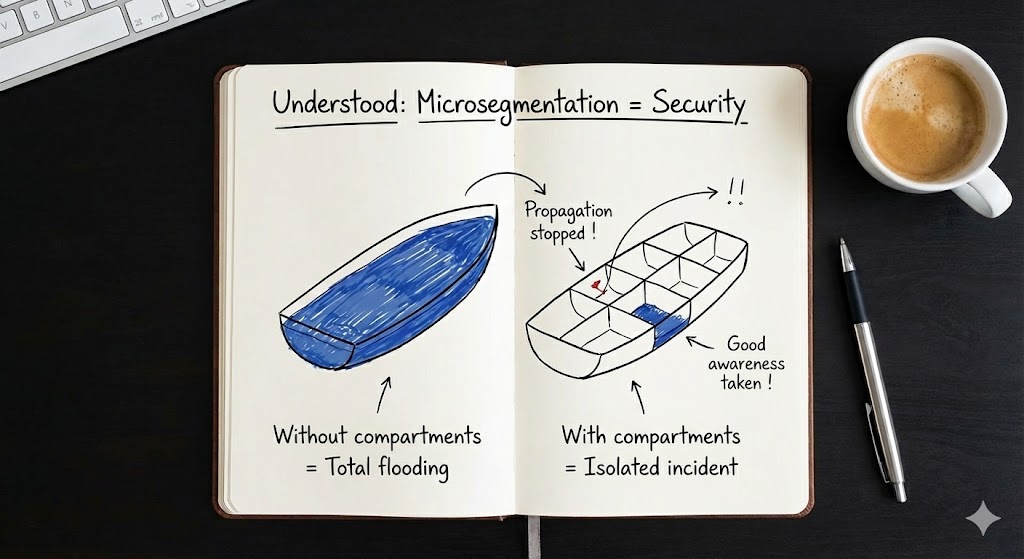
Microsegmentation in one picture
Without compartments: flooding spreads everywhere. With compartments: the incident stays contained.
Lateral movement protection¶
Lateral movement is what an attacker does after an initial compromise: moving from one workload to another to reach higher-value targets.
Common techniques:
- Reusing credentials
- Exploiting open admin ports
- Pivoting through shared services
- Scanning internal ranges
How microsegmentation helps¶
- Default posture: deny by default (or highly restricted)
- Allow only required flows (application dependencies)
- Policies expressed using labels (scope, app, env, role, location, etc.)
- Enforcement happens close to the workload (agent-based), not only at the perimeter
Key idea
Microsegmentation is not “block everything”. It is “allow only what is required”.
Outcomes: reduce risk exposure¶
- Reduce risk exposure and limit incident spread
- Contain incidents faster
- Improve visibility of “who talks to whom”
What this changes operationally¶
- Applications are treated as scopes (combination of labels)
- Onboarding becomes a structured process (workshops + flow validation)
- Changes follow a controlled workflow (change-management + approvals when required)